Latest Facts
Sports
Society
Sports
Celebrity
Society
Society
Sports
Sports
Technology
Society
Games and Toys
Society
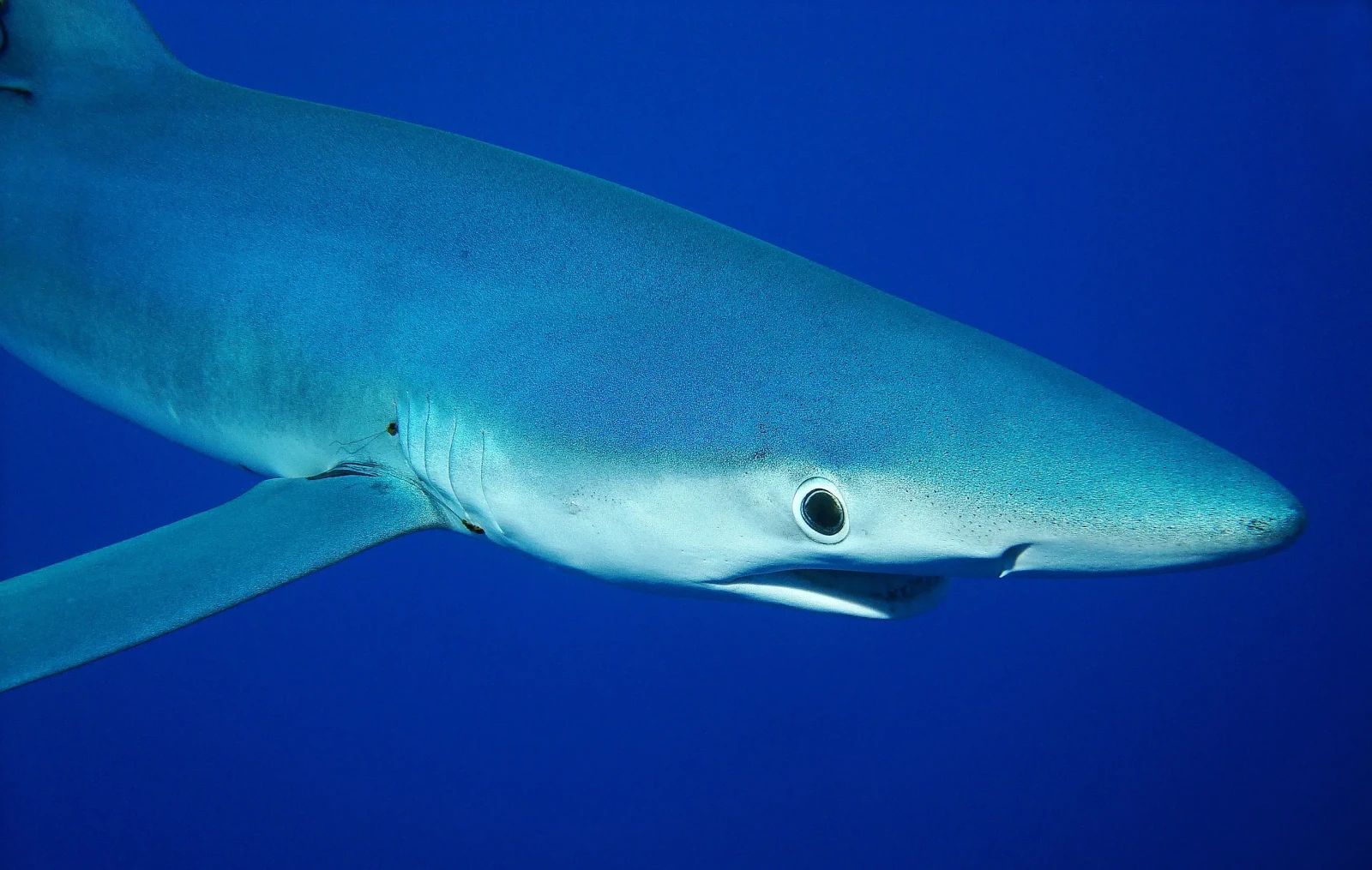
Health Science
Sports
General
Characters
Celebrity
Society
Society
Technology
Celebrity
Sports
Entertainment
Sports
Sports
General
Performing Arts
People
Celebrity
Sports
Celebrity
Popular Facts

25 Legendary Hockey Players
What makes a hockey player legendary? Is it their astonishing skills, their record-breaking stats, or perhaps their unforgettable moments on the ice? Hockey has seen countless players who have left […]